Principles of Information Security Chapter 4 Review Questions
Principles of Information Security, Quaternary Edition Chapter 4 Managing IT Gamble
Learning Objectives • Upon completion of this cloth, you should be able to: – Define risk management, chance identification, and gamble command – Depict how risk is identified and assessed – Assess take a chance based on probability of occurrence and likely impact – Explain the fundamental aspects of documenting take a chance via the process of risk assessment Principles of Information Security, Quaternary Edition 2
Learning Objectives (cont'd. ) – Describe the diverse run a risk mitigation strategy options – Identify the categories that can be used to classify controls – Recognize the conceptual frameworks for evaluating risk controls and codify a cost benefit assay – Describe how to maintain and perpetuate/sustain risk controls Principles of Information Security, Fourth Edition 3
Introduction • Organizations must design and create safety environments in which business processes and procedures can function • Risk management: process of identifying and decision-making risks facing an organization • Risk identification: procedure of examining an arrangement's electric current it security situation • Risk control: applying controls to reduce risks to an organization's data and information systems Principles of Information Security, Fourth Edition four
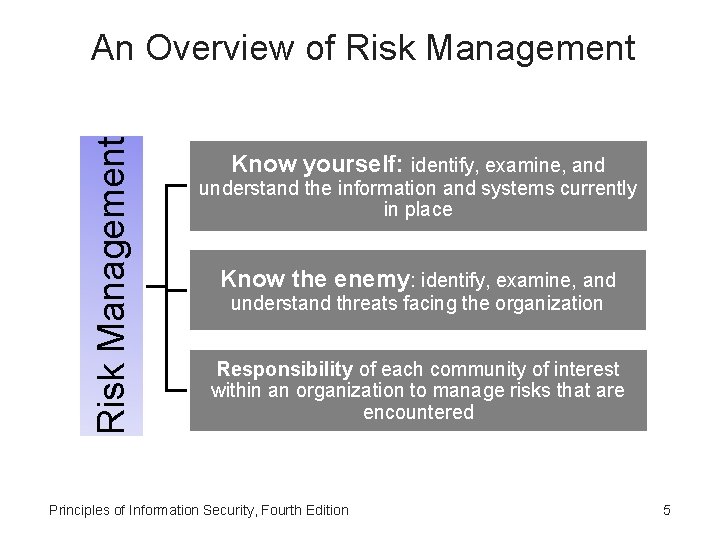
Take a chance Management An Overview of Hazard Direction Know yourself: identify, examine, and understand the data and systems currently in place Know the enemy: place, examine, and understand threats facing the organization Responsibility of each community of involvement inside an arrangement to manage risks that are encountered Principles of Information Security, Quaternary Edition v
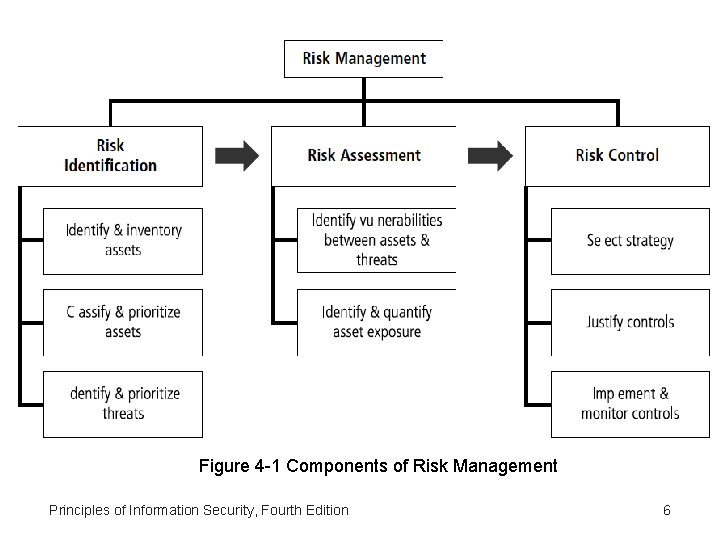
Figure 4 -1 Components of Adventure Direction Principles of Information Security, 4th Edition 6
The Roles of the Communities of Interest • Information security, direction and users, and information technology all must work together • Communities of interest are responsible for: – Evaluating the take chances controls – Determining which command options are cost effective for the organization – Acquiring or installing the needed controls – Ensuring that the controls remain constructive Principles of Information Security, Fourth Edition seven
Take a chance Identification • Risk management involves 1 - identifying two - classifying three -prioritizing an organization'southward assets • A threat assessment process identifies and quantifies the risks facing each asset • Components of take a chance identification – People – Procedures – Data – Software – Hardware Principles of Data Security, Quaternary Edition viii
Plan and Organize the Process • First step in the Risk Identification procedure is : follow your project direction principles • Begin past organizing a team with representation across all affected groups • The process must and then exist planned out – Periodic deliverables – Reviews – Presentations to management • Tasks laid out, assignments made and timetables discussed Principles of Information Security, 4th Edition 9
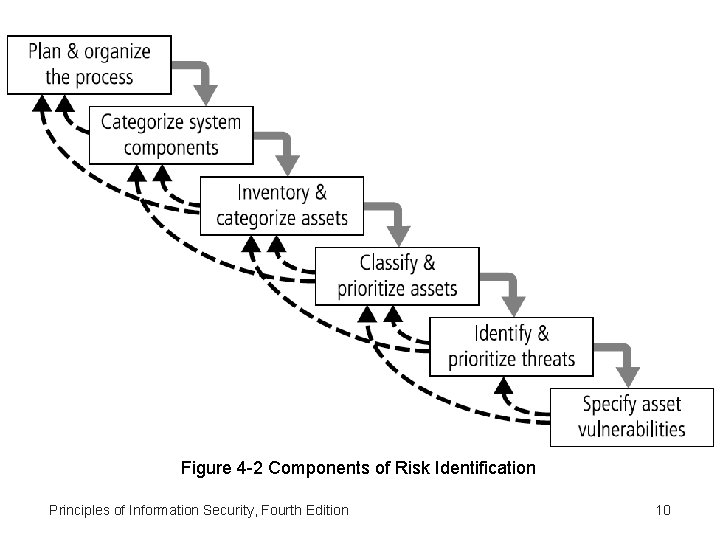
Figure iv -2 Components of Risk Identification Principles of Information Security, Fourth Edition 10
Asset Identification and Inventory • Iterative process; begins with identification of assets, including all elements of an organization'south system (people, procedures, data and information, software, hardware, networking) • Assets are and then classified and categorized Principles of Data Security, Fourth Edition 11
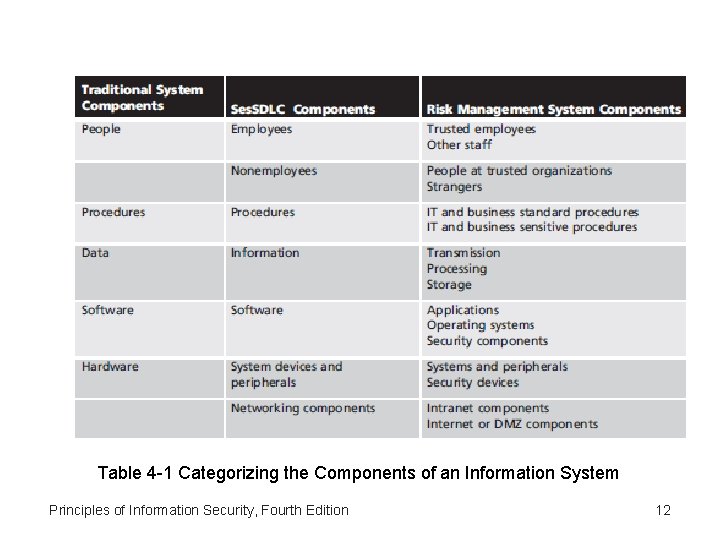
Table 4 -1 Categorizing the Components of an Information Arrangement Principles of Information Security, Fourth Edition 12
People, Procedures, and Data Asset Identification • Man resources, documentation, and data information avails are more hard to identify • Important asset attributes: – People: position name/number/ID; supervisor; security clearance level; special skills – Procedures: description; intended purpose; what elements it is tied to; storage location for reference; storage location for update – Data: classification; owner/creator/ manager; data structure size; data structure used; online/offline; location; backup procedures employed Principles of Information Security, Fourth Edition 13
Hardware, Software, and Network Asset Identification • What information attributes to track depends on: – Needs of arrangement/risk direction efforts – Preferences/needs of the security and data technology communities • Asset attributes to exist considered are: name; IP address; MAC accost; chemical element type; serial number; manufacturer name; model/part number; software version; concrete or logical location; decision-making entity • Automated tools tin place system elements for hardware, software, and network components Principles of Information Security, Fourth Edition 14
Data Classification and Direction • Variety of nomenclature schemes used by corporate and military organizations • Information owners responsible for classifying their information assets • Information classifications must be reviewed periodically • Most organizations do not demand detailed level of nomenclature used by war machine or federal agencies; however, organizations may need to classify data to provide protection Principles of Information Security, 4th Edition 15
Data Classification and Management (cont'd. ) • Security clearance structure – Each data user assigned a unmarried level of authorisation indicating classification level – Before accessing specific set of data, employee must meet need-to-know requirement • Management of Classified Information • Storage, distribution, portability, and destruction of classified data • Make clean desk policy • Dumpster diving Principles of Information Security, Fourth Edition sixteen
Classifying and Prioritizing Information Assets • Many organizations have data classification schemes (eastward. g. , confidential, internal, public data) • Classification of components must be specific to allow determination of priority levels • Categories must be comprehensive and mutually exclusive Principles of Information Security, Fourth Edition 17
Information Nugget Valuation • Questions help develop criteria for asset valuation • Which information asset: – – Is most critical to organization's success? Generates the most revenue/profitability? Would be almost expensive to replace or protect? Would exist the most embarrassing or cause greatest liability if revealed? Principles of Information Security, 4th Edition xviii
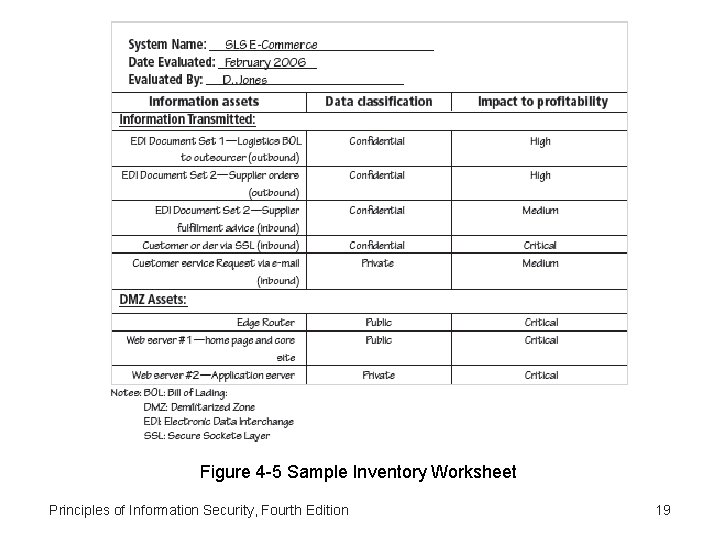
Effigy 4 -5 Sample Inventory Worksheet Principles of Information Security, Fourth Edition nineteen
Information Asset Valuation (cont'd. ) • Data asset prioritization – Create weighting for each category based on the answers to questions – Summate relative importance of each asset using weighted factor analysis – List the assets in social club of importance using a weighted factor analysis worksheet Principles of Information Security, Quaternary Edition 20
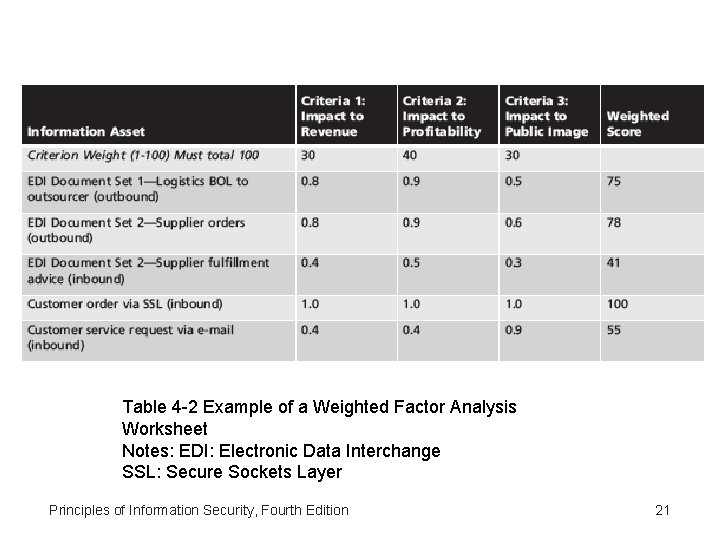
Table 4 -2 Example of a Weighted Factor Assay Worksheet Notes: EDI: Electronic Data Interchange SSL: Secure Sockets Layer Principles of Information Security, Fourth Edition 21
Identifying and Prioritizing Threats • Realistic threats demand investigation; unimportant threats are set aside • Threat assessment: – Which threats present danger to assets? – Which threats stand for the most danger to information? – How much would it price to recover from attack? – Which threat requires greatest expenditure to forestall? Principles of Information Security, Fourth Edition 22
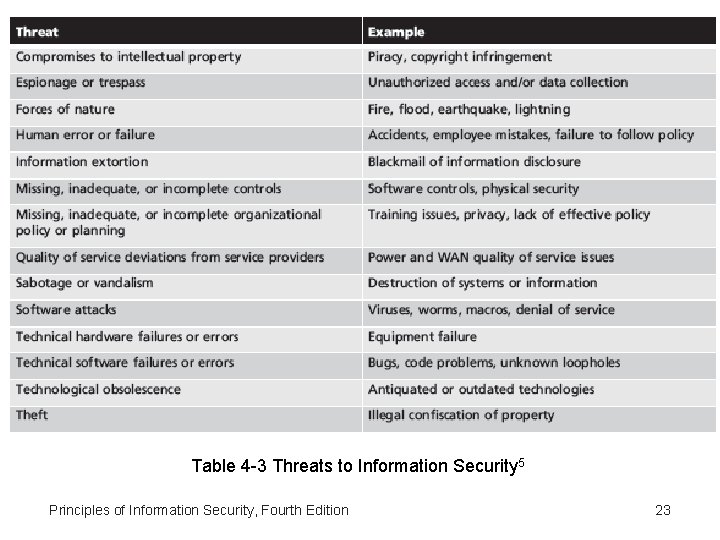
Tabular array 4 -3 Threats to Information Security five Principles of Data Security, Fourth Edition 23
Vulnerability Identification • Specific avenues threat agents tin exploit to attack an information asset are called vulnerabilities • Examine how each threat could exist perpetrated and listing organization's avails and vulnerabilities • Process works all-time when people with diverse backgrounds within organization work iteratively in a serial of brainstorming sessions • At cease of risk identification procedure, list of assets and their vulnerabilities is achieved Principles of Information Security, 4th Edition 24
Risk Assessment • Chance cess evaluates the relative chance for each vulnerability • Assigns a take a chance rating or score to each data asset • The goal at this signal: create a method for evaluating the relative risk of each listed vulnerability Principles of Data Security, Fourth Edition 25
Likelihood • The probability that a specific vulnerability will be the object of a successful attack • Assign numeric value: number betwixt 0. 1 (low) and 1. 0 (loftier), or a number between i and 100 • Zero not used since vulnerabilities with nada likelihood are removed from asset/vulnerability listing • Use selected rating model consistently • Employ external references for values that accept been reviewed/adjusted for your circumstances Principles of Information Security, Fourth Edition 26
Risk Conclusion • For the purpose of relative risk assessment: – – – Risk EQUALS Likelihood of vulnerability occurrence TIMES value (or bear upon) MINUS percentage risk already controlled PLUS an chemical element of doubtfulness – Take a chance = (likelihood * value or impact) – (pct risk already controlled) + (dubiety element ) Principles of Information Security, Fourth Edition 27
Identify Possible Controls • For each threat and associated vulnerabilities that have residual chance, create preliminary list of control ideas • Residual risk is take a chance that remains to information nugget fifty-fifty after existing control has been applied • At that place are 3 general categories of controls: – Policies – Programs – Technologies Principles of Information Security, Quaternary Edition 28
Documenting the Results of Risk Assessment • Concluding summary comprised in ranked vulnerability risk worksheet • Worksheet details asset, asset impact, vulnerability likelihood, and risk-rating factor • Ranked vulnerability risk worksheet is initial working document for next step in risk management process: assessing and controlling take chances Principles of Information Security, Fourth Edition 29
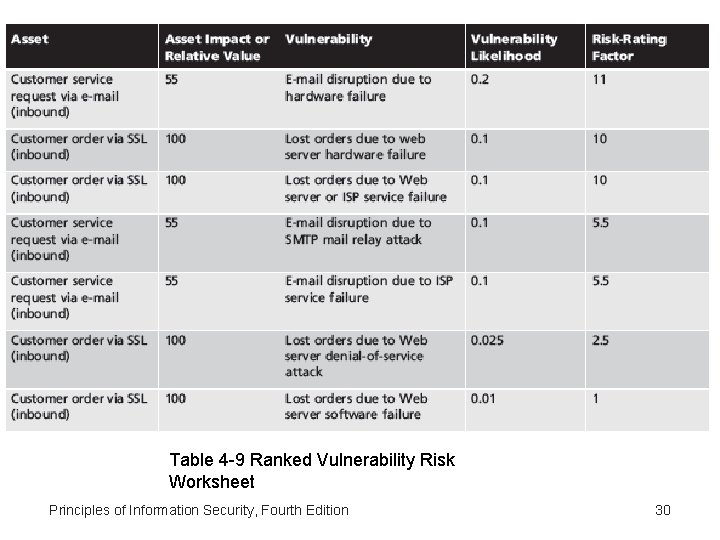
Tabular array 4 -ix Ranked Vulnerability Gamble Worksheet Principles of Information Security, Fourth Edition 30
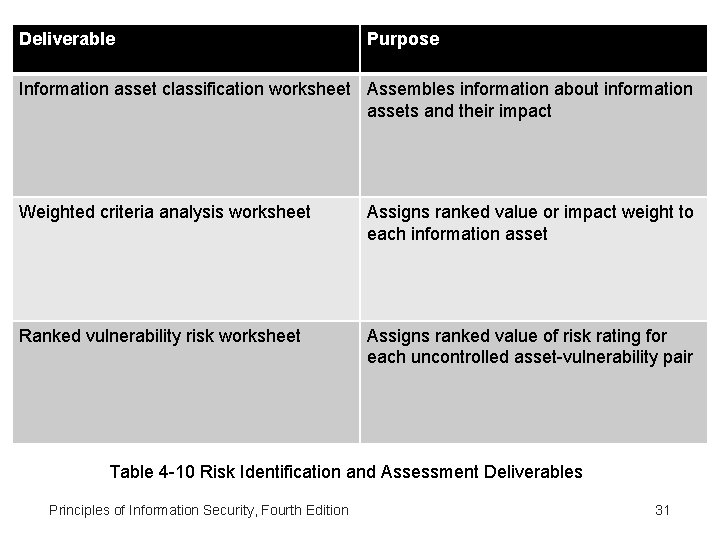
Deliverable Purpose Information nugget classification worksheet Assembles data nearly information assets and their bear upon Weighted criteria assay worksheet Assigns ranked value or impact weight to each data asset Ranked vulnerability adventure worksheet Assigns ranked value of hazard rating for each uncontrolled asset-vulnerability pair Table 4 -10 Risk Identification and Assessment Deliverables Principles of Information Security, Fourth Edition 31
Take a chance Control Strategies • One time ranked vulnerability adventure worksheet complete, must choose 1 of five strategies to control each risk: – – – Defend Transfer Mitigate Accept Terminate Principles of Information Security, Fourth Edition 32
Defend • Attempts to preclude exploitation of the vulnerability • Preferred approach • Accomplished through countering threats, removing nugget vulnerabilities, limiting asset admission, and adding protective safeguards • Three common methods of risk avoidance: – Application of policy – Grooming and education – Applying technology Principles of Information Security, Fourth Edition 33
Transfer • Control approach that attempts to shift take chances to other avails, processes, or organizations • If lacking, organization should hire individuals/firms that provide security management and assistants expertise • Organisation may then transfer hazard associated with direction of complex systems to another organization experienced in dealing with those risks Principles of Information Security, Fourth Edition 34
Mitigate • Attempts to reduce touch on of vulnerability exploitation through planning and preparation • Approach includes three types of plans – Incident response programme (IRP): define the actions to take while incident is in progress – Disaster recovery plan (DRP): most common mitigation procedure – Business organisation continuity plan (BCP): encompasses continuation of concern activities if catastrophic upshot occurs Principles of Information Security, Quaternary Edition 35
Have • Doing nothing to protect a vulnerability and accepting the outcome of its exploitation • Valid simply when the particular function, service, information, or asset does not justify price of protection Principles of Information Security, 4th Edition 36
Terminate • Directs the organization to avert those business activities that introduce uncontrollable risks • May seek an alternate mechanism to meet customer needs Principles of Information Security, 4th Edition 37
Selecting a Risk Command Strategy • Level of threat and value of asset play major role in choice of strategy • Rules of pollex on strategy selection tin be applied: – – When a vulnerability exists When a vulnerability tin can be exploited When assailant's price is less than potential proceeds When potential loss is substantial Principles of Data Security, 4th Edition 38
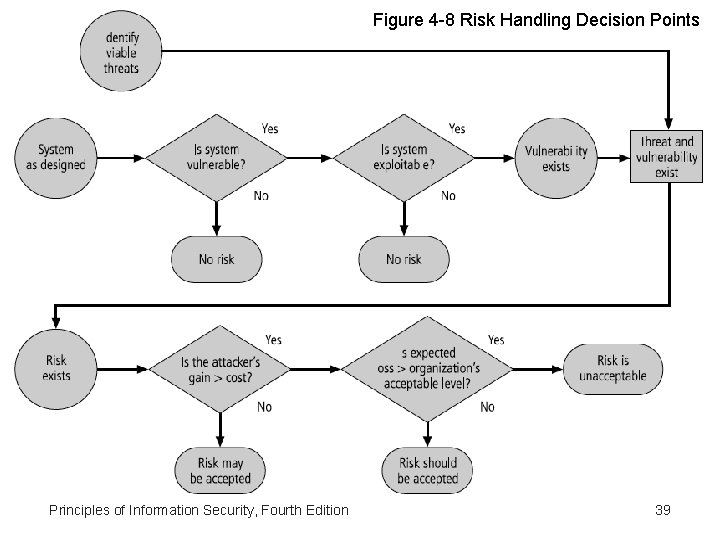
Figure four -8 Gamble Handling Decision Points Principles of Data Security, Fourth Edition 39
Feasibility Studies • Earlier deciding on strategy, all data about economic/noneconomic consequences of vulnerability of data nugget must exist explored • A number of ways be to determine advantage of a specific control Principles of Data Security, Fourth Edition 40
Price Benefit Analysis (CBA) • Begun by evaluating worth of assets to be protected and the loss in value if they are compromised • The formal process to certificate this is called cost do good analysis or economic feasibility written report • Items that affect price of a command or safeguard include: – – – cost of development or acquisition; training fees; implementation cost; service costs; price of maintenance • Benefit: value an organization realizes using controls to prevent losses from a vulnerability Principles of Data Security, Quaternary Edition 41
Toll Benefit Assay (CBA) (cont'd. ) • Asset valuation: procedure of assigning fiscal value or worth to each information asset • Process result is estimate of potential loss per risk • Expected loss per risk stated in the following equation: – Annualized loss expectancy (ALE) = single loss expectancy (SLE) × annualized rate of occurrence (ARO) – SLE = asset value × exposure cistron (EF) Principles of Data Security, Fourth Edition 42
The Cost Benefit Analysis (CBA) Formula • CBA determines if alternative being evaluated is worth cost incurred to control vulnerability – CBA almost easily calculated using ALE from earlier assessments, before implementation of proposed control: • CBA = ALE(prior) – ALE(post) – ACS – ALE(prior) is Annualized Loss Expectancy of risk before implementation of command – ALE(post) is estimated ALE based on command being in place for a period of time – ACS is the Annualized Cost of the Safeguard Principles of Information Security, Fourth Edition 43
Evaluation, Assessment, and Maintenance of Hazard Controls • Selection and implementation of command strategy is not end of process • Strategy and accompanying controls must exist monitored/reevaluated on ongoing basis to decide effectiveness and to calculate more accurately the estimated residual risk • Procedure continues as long as arrangement continues to office Principles of Data Security, Fourth Edition 44
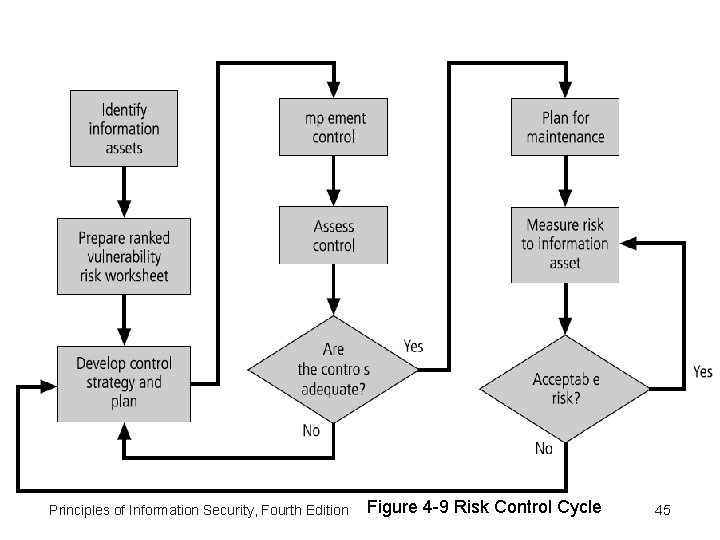
Principles of Information Security, Fourth Edition Figure iv -9 Run a risk Control Cycle 45
Quantitative Versus Qualitative Gamble Control Practices • Performing the previous steps using actual values or estimates is known every bit Quantitative Assessment • Qualitative Assessment : Possible to complete steps using evaluation process based on characteristics using non-numerical measures. • Scales importance : Utilizing scales rather than specific estimates relieves system from difficulty of determining exact values Principles of Information Security, Fourth Edition 46
Benchmarking and Best Practices • An alternative approach to risk management • Benchmarking: procedure of seeking out and studying practices in other organizations that 1's ain organization desires to duplicate • One of ii measures typically used to compare practices: – Metrics-based measures – Process-based measures • In information security, two categories of benchmarks are used: standards of due care/due diligence and best practices. • In and all-time practices , the Gold Exercise == "the best of the all-time. " Principles of Information Security, Fourth Edition 47
Benchmarking and All-time Practices (cont'd. ) • Standard of due care: when adopting levels of security for a legal defense, organisation shows it has done what whatsoever prudent organization would do in similar circumstances • Due diligence: demonstration that arrangement is diligent in ensuring that implemented standards continue to provide required level of protection • Failure to support standard of due intendance or due diligence can get out organization open to legal liability Principles of Information Security, Fourth Edition 48
Benchmarking and Best Practices (cont'd. ) • All-time business organization practices: security efforts that provide a superior level of information protection • When considering best practices for adoption in an organization, consider: – Does organization resemble identified target with all-time exercise? – Are resources at hand similar? – Is organisation in a similar threat surroundings? Principles of Information Security, Fourth Edition 49
Benchmarking and All-time Practices (cont'd. ) • Issues with the application of benchmarking and best practices – Organizations don't talk to each other (biggest problem) – No two organizations are identical – Best practices are a moving target – Knowing what was going on in information security industry in recent years through benchmarking doesn't necessarily gear up for what'south next Principles of Information Security, Quaternary Edition 50
Benchmarking and All-time Practices (cont'd. ) • Baselining: – Is Assay of measures against established standards – In information security, baselining is comparison of security activities and events against an system's future functioning – Useful during baselining to have a guide to the overall process Principles of Information Security, Fourth Edition 51
Other Feasibility Studies • Organizational: examines how well proposed IS alternatives volition contribute to organization's efficiency, effectiveness, and overall operation • Operational: examines user and management acceptance and support, and the overall requirements of the organization's stakeholders • Technical: examines if organization has or tin acquire the technology necessary to implement and support the command alternatives • Political: defines what tin can/cannot occur based on consensus and relationships Principles of Data Security, Fourth Edition 52
Risk Management Discussion Points • Organisation must define level of risk it can live with • Risk appetite: defines quantity and nature of risk that organizations are willing to accept as merchandise-offs between perfect security and unlimited accessibility • Residue risk: run a risk that has not been completely removed, shifted, or planned for Principles of Data Security, 4th Edition 53
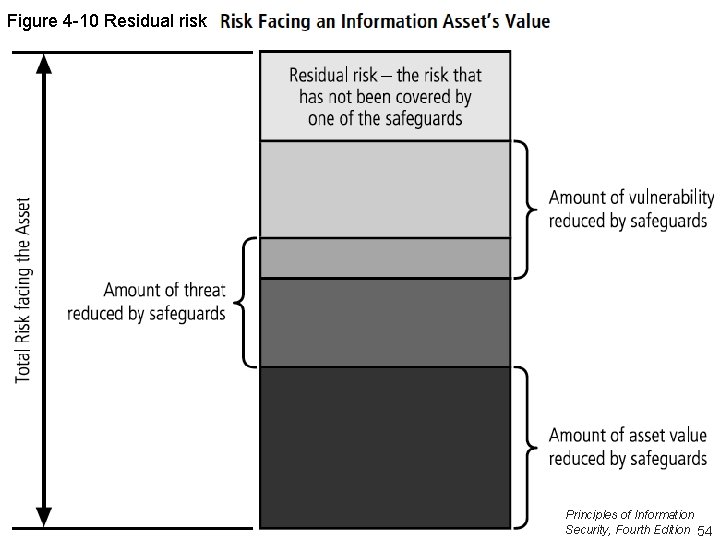
Figure 4 -10 Residual hazard Principles of Information Security, Quaternary Edition 54
Documenting Results • At minimum, each information asset-threat pair should have documented control strategy clearly identifying any remaining residual risk • Some other pick: document outcome of control strategy for each information nugget-vulnerability pair as an action plan • Risk assessment may exist documented in a topicspecific study Principles of Information Security, Fourth Edition 55
Recommended Hazard Control Practices • Convince budget regime to spend up to value of asset to protect from identified threat • Final control selection may be residue of controls providing greatest value to equally many asset-threat pairs every bit possible • Organizations looking to implement controls that don't involve such complex, inexact, and dynamic calculations Principles of Information Security, Fourth Edition 56
Summary • Chance identification: formal process of examining and documenting risk in data systems • Chance control: process of taking carefully reasoned steps to ensure the confidentiality, integrity, and availability of components of an information organization • Hazard identification – A hazard management strategy enables identification, classification, and prioritization of arrangement'southward data assets – Residue risk: risk remaining to the information asset even after the existing control is practical Principles of Information Security, Fourth Edition 57
Summary (connected) • Gamble command: v strategies are used to control risks that event from vulnerabilities: – – – Defend Transfer Mitigate Accept Terminate Principles of Information Security, Fourth Edition 58
Summary (continued) • Selecting a gamble control strategy – Price Benefit Assay – Feasibility Study • Qualitative versus Quantitative Risk Control – All-time Practices and Benchmarks – Organizational Feasibility, Operational Feasibility, Technical Feasibility, and Political Feasibility • Take a chance Appetite: organizational risk tolerance • Residual risk: risk remaining later application of take chances controls Principles of Information Security, Fourth Edition 59
hoffmancourbeacced.blogspot.com
Source: https://slidetodoc.com/principles-of-information-security-fourth-edition-chapter-4/
0 Response to "Principles of Information Security Chapter 4 Review Questions"
Post a Comment